Enhanced Mitigation Experience Toolkit
EMET is a free tool built to offer additional security defenses against vulnerable third party applications and assorted vulnerabilities. EMET helps prevent vulnerabilities in software from being successfully exploited by using security mitigation technologies. These technologies function as special protections and obstacles that an exploit author must defeat to exploit software vulnerabilities. These security mitigation technologies work to make exploitation as difficult as possible to perform but do not guarantee that vulnerabilities cannot be exploited.
Download the tool here
and the User’s guide here.
Installing EMET
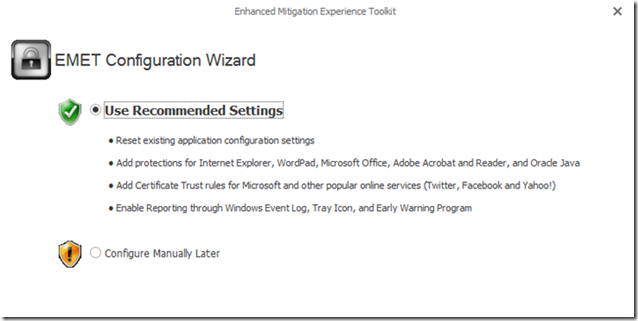
Install the tool and start with the recommended settings.
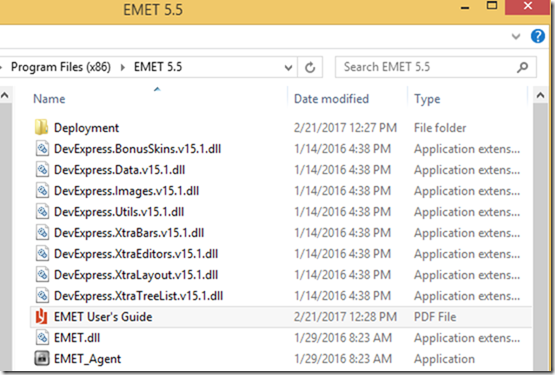
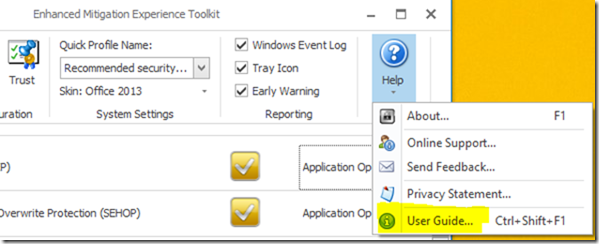
Rename the file “EMET 5.5 User’s Guide.pdf” to “EMET User’s Guide.pdf” and copy/move it to the EMET 5.5 installation folder.
Now you can open it from within the application.
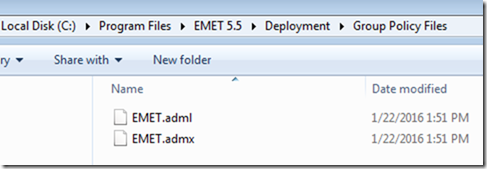
Once EMET is deployed, system administrators can use the provided template files for security configuration. The EMET.admx and EMET.adml files are located in the “Deployment\Group Policy Files” folder.
These files must be copied onto \Windows\PolicyDefinitions and \Windows\PolicyDefinitions\en-US folders respectively. Once this is done, EMET settings can be configured via Group Policy.
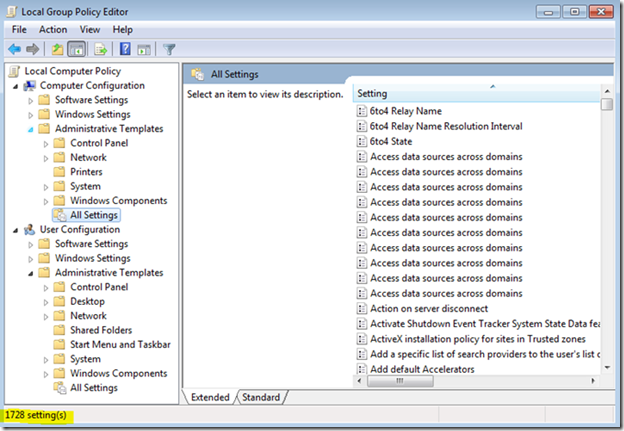
Before installing the EMET templates, Windows has
- 1728 Computer Configuration settings
- 1514 User Configuration settings
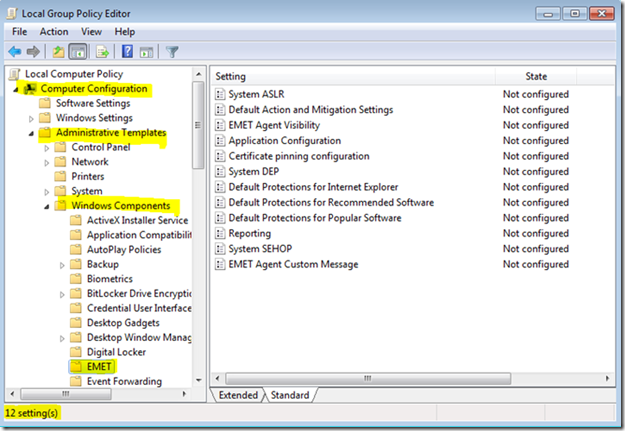
Additional settings after installing the EMET templates:
and
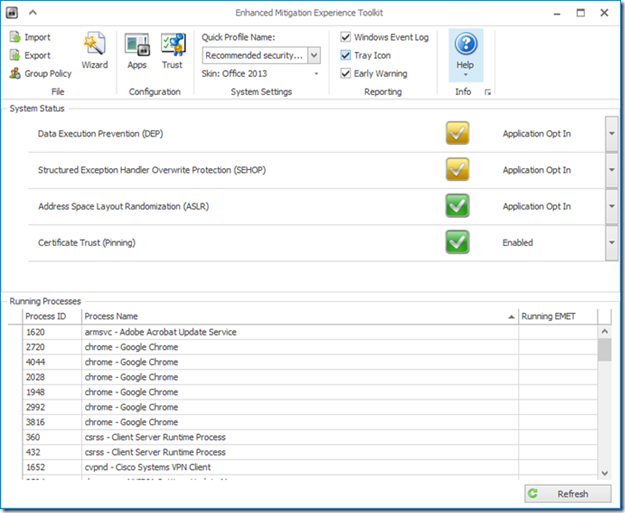
Using the EMET Tool
EMET must be configured after installation, for the security mitigations to be enabled. To configure EMET, the following parameters have to be specified:
- Which system mitigations should be enabled;
- Which applications should be protected with which mitigations;
- What SSL/TLS certificate pinning rules to adopt.
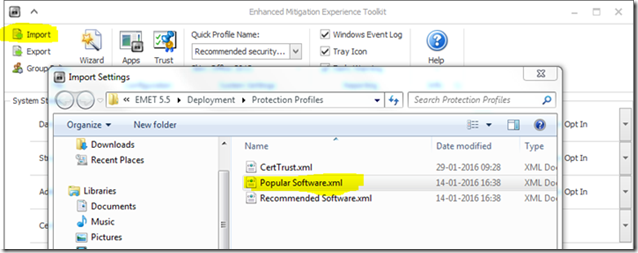
Upon installation, EMET will have a list of applications to be protected. However, you can add any application you want to that list. Press the “Import” button and select the “Popular Software.xml” file provided with EMET.
This file adds additional rules to help protect popular third-party programs like Firefox, Chrome, Skype, iTunes, Photoshop, Thunderbird, Opera, Google Talk, Pidgin, VLC, WinRAR, and 7-Zip.
EMET provides a way to turn on Address Space Layout Randomization, Data Execution Prevention, as well as other security features for applications that don’t specifically request them. It’s not an included Windows feature because it could potentially break some programs and most users wouldn’t know how to fix such problems.
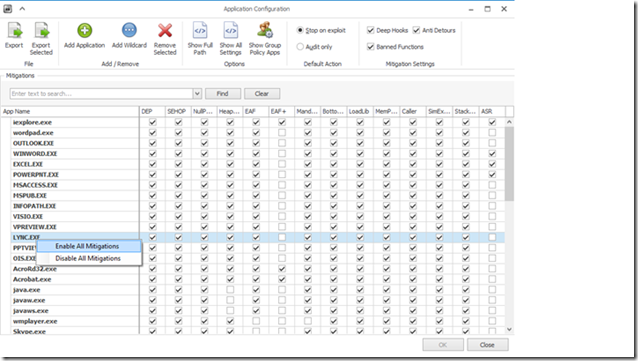
You can view the rules installed on your system by clicking the Apps button under Configuration in the ribbon at the top of the window. Your computer should now be more secure than it was before.
ASLR randomizes the locations of applications and system libraries in memory making it extremely difficult for an attacker to create reliable exploits that depend on knowing exactly where certain code is in memory.
DEP allows the operating system to mark certain sections of memory as non-executable data. If an attacker takes advantage of a buffer overflow vulnerability in an application and attempts to run code from a sector marked as data, the operating system won’t run it.
Blocking Other Applications
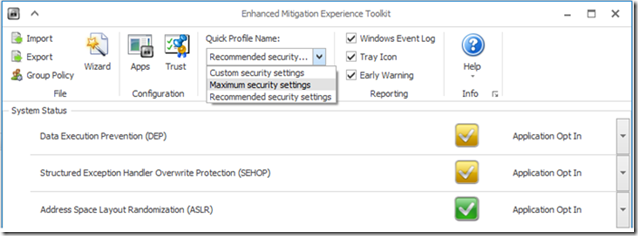
EMET allows you to activate more security features on your own. Try clicking the “Quick Profile Name” box and selecting “Maximum Security Settings”. This will enable DEP for all applications and enable Structured Exception Handler Overwrite Protection (SEHOP) for applications that don’t specifically opt out of it.
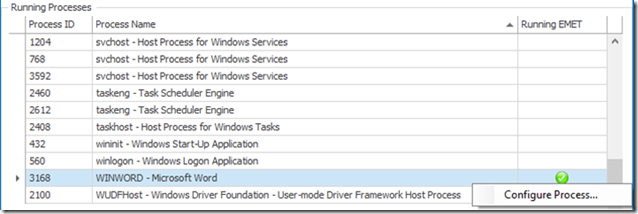
To help protect a specific application, right-click it in the list of running processes and select “Configure Process”. You’ll be able to set various rules to help lock it down. For technical information on exactly what each security feature does, refer to the EMET User’s Guide.
These protections aren’t enabled by default because they may cause some applications to not work properly. If an application breaks, go back into EMET, disable certain security features for it, and see if the application works. If you changed a system-wide setting and an application no longer works properly, change the system setting back or add a special exception for that application.
System administrators could use EMET to test if an application works, export the rule, and then import it on other PCs running EMET to roll out their tested rules. Use the Export or Export Selected options to export rules you’ve created.
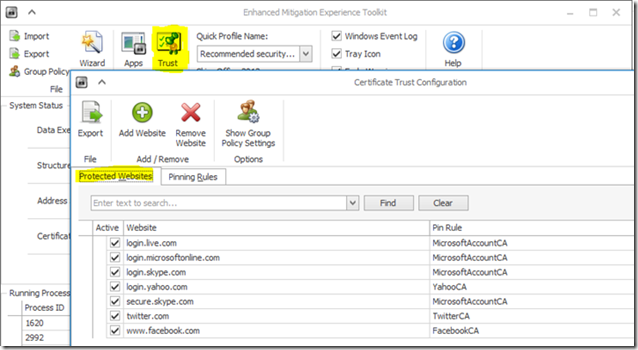
EMET also provides a configurable SSL/TLS certificate pinning feature that is called Certificate Trust. This feature is intended to detect and stop man-in-the-middle attacks that are leveraging the public key infrastructure (PKI).
Once enabled, users have to specify which certificates and Root Certificate Authorities to trust. Each time a certificate chain trust is built by Internet Explorer for a SSL certificate while browsing to an HTTPS website for which certificate pinning is configured, EMET will validate the end-entity SSL certificate and verify that it chains to the Root CA specified by the pinning rule configured for that site.
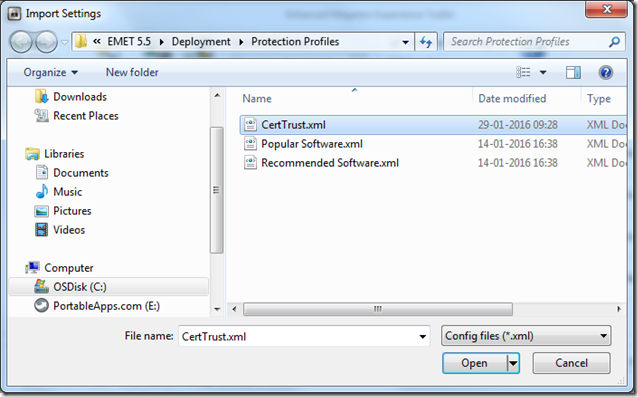
Importing the “CertTrust.xml” will enables certificate pinning rules for the login services of Microsoft Account, Microsoft Office 365, and Skype, and other popular online services such as Twitter, Facebook, and Yahoo!.
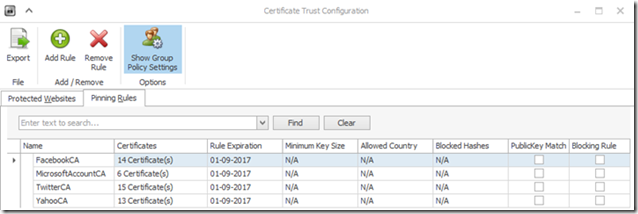
Certificate pinning rules:
Policy Analyzer
Whatever the method you used to adjust your configuration, you can also use another Microsoft tool that will allow to get an overall picture of your system’s status, the Policy Analyzer.
Policy Analyzer is a free utility for analyzing and comparing sets of Group Policy Objects (GPOs).
- It can compare GPOs against current local policy settings and against local registry settings.
- It can highlight when a set of Group Policies has redundant settings or internal inconsistencies
- It can highlight the differences between versions or sets of Group Policies.
- It can treat a set of GPOs as a single unit making it easy to determine whether particular settings are duplicated across the GPOs or are set to conflicting values.
- It can capture a baseline and then compare it to a snapshot taken at a later time to identify changes anywhere across the set.
- It can export its findings to a Microsoft Excel spreadsheet.
Create a Baseline
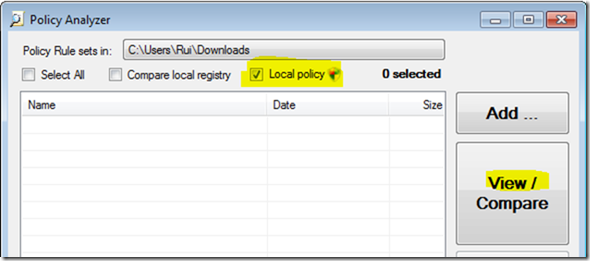
View implemented local policies:
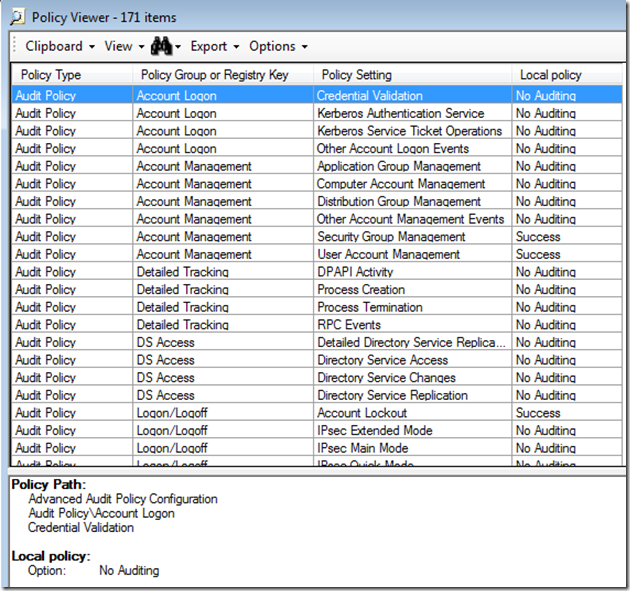
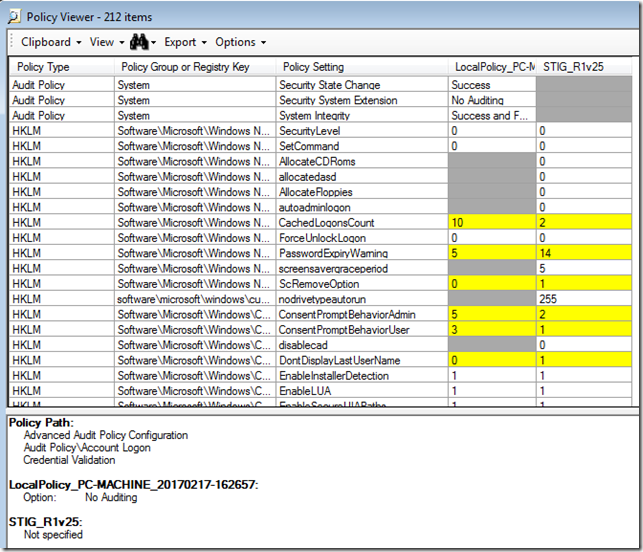
Spreadsheet style results:
Compare the Baseline with existing standards
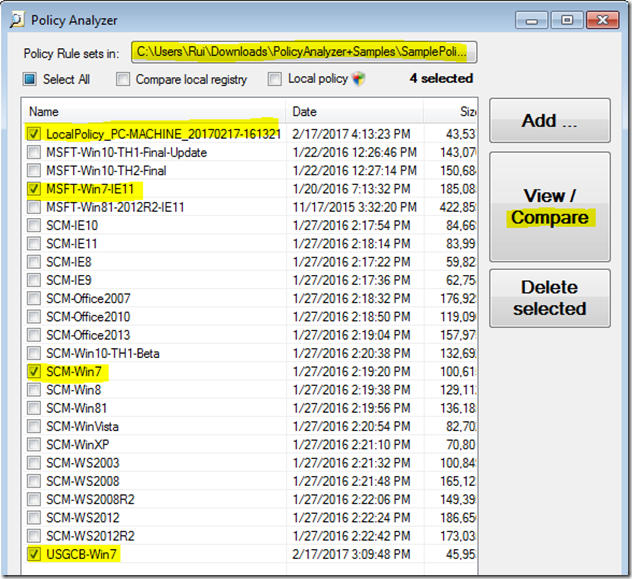
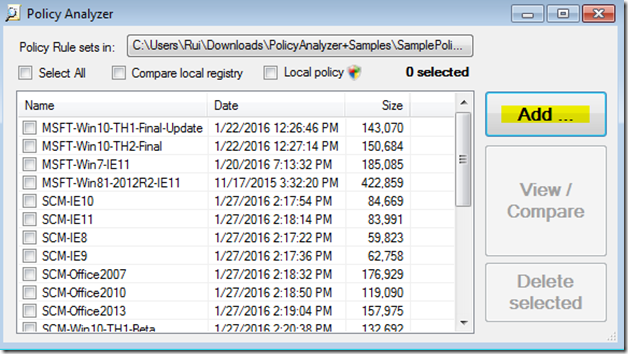
Set the appropriate directory for the sample Policy Rules
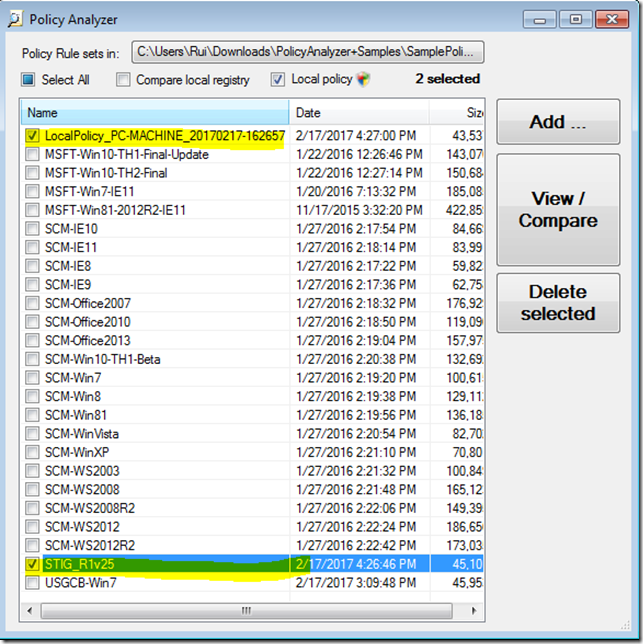
Compare the local policy, generated in the previous steps, with:
- Microsoft settings for IE 11
- Security Compliance Manager setting for Windows 7
- US Government configuration baseline for Windows 7
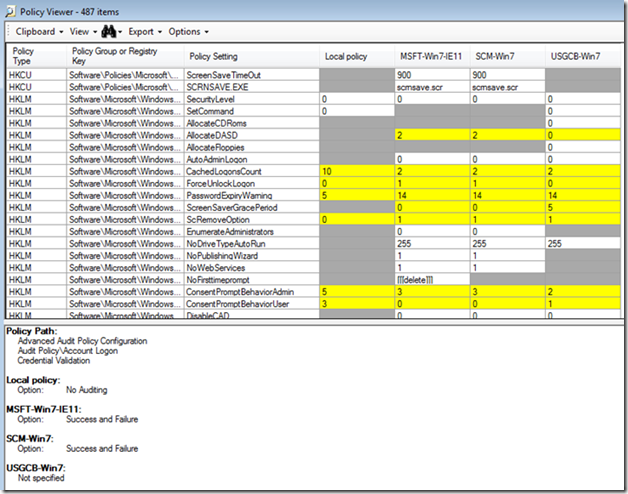
Compliance results:
Compare baseline with the STIG
Create a new rule for the latest STIG
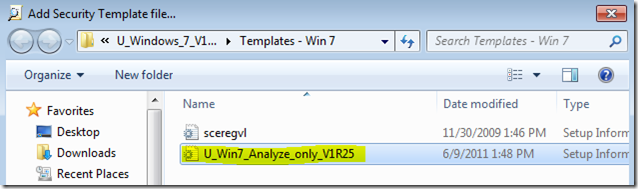
Import the security template provided with the STIG
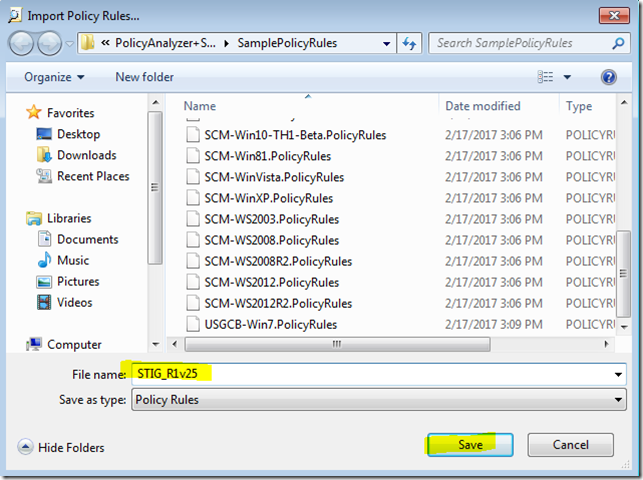
Save it next to the other Policy Rules
Run a new comparison analysis
STIG compliance results:
Previous post: Windows 7 Hardening (Part I)
Next post: Linux Hardening with Tiger



2 comments:
Good Bolg. Oracle Fusion SCM Online Training
PUG PUPPY ADOPTION
Pug puppies for sale
Pug puppies for sale near me
Pug puppiesfor sale near me
Available pug puppies for sale
Black Pug Puppies for sale
Post a Comment