Using the STIG templates
Just like in previous version of Windows, some of the requirements in the Windows 10 STIG depend on the use of additional group policy administrative templates that are not included with Windows by default. The new administrative template files (.admx and .adml file types) must be copied to the appropriate location in the Windows directory to make the settings they provide visible in group policy tools.
This includes settings under MS Security Guide, MSS (Legacy), and the Enhanced Mitigation Experience Toolkit (EMET) tool. The MSS settings have previously been made available through an update of the Windows security options file (sceregvl.inf). This required a change in permissions to that file, which is typically controlled by the system. A custom template was developed to avoid this.
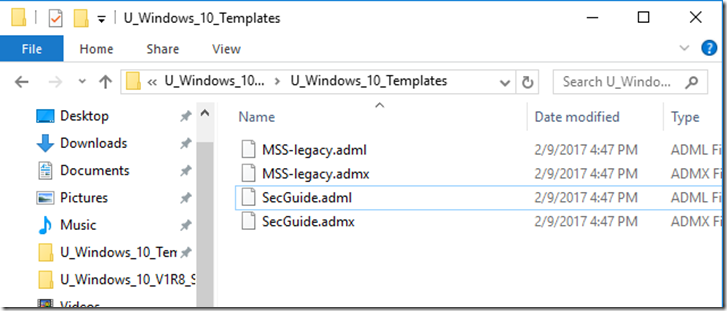
The custom template files (MSS-Legacy and SecGuide) are provided in the Templates directory of the STIG package. The EMET administrative template files are located in the tool’s installation directory, typically “\Program Files (x86)\EMET x.x\Deployment\Group Policy Files\”.
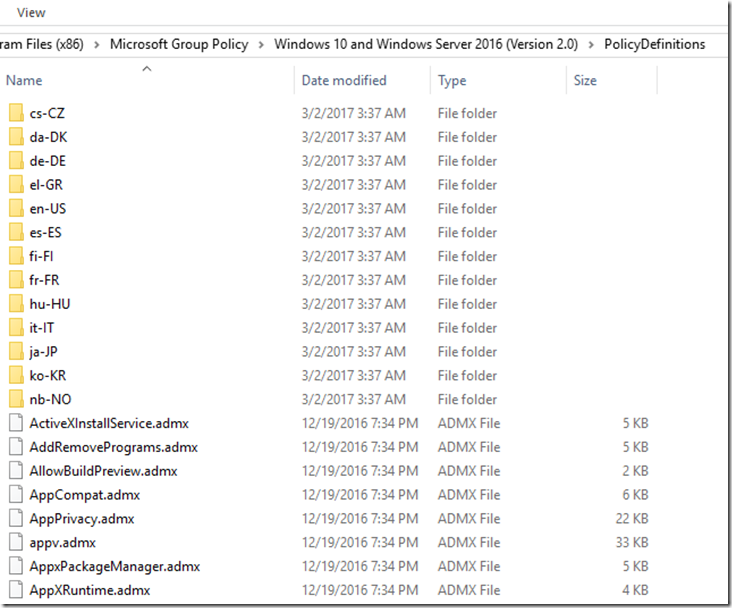
The .admx files must be copied to the \Windows\PolicyDefinitions\ directory. The .adml files must be copied to the \Windows\PolicyDefinitions\en-US\ directory.
NOTE: EMET’s end of life date is being extended until July 31, 2018a and at this time there are no plans to offer support or security patching for EMET that date. For improved security, everyone should migrate to the latest version of Windows 10. EMET 5.5 is compatible with current versions of Windows 10 but according to this article, it won’t be compatible with future versions of the latest Microsoft OS.
Before the installation of the STIG templates, Windows 10 Enterprise has:
- 2283 Computer configuration settings
- 1731 User configuration settings
The STIG Templates:
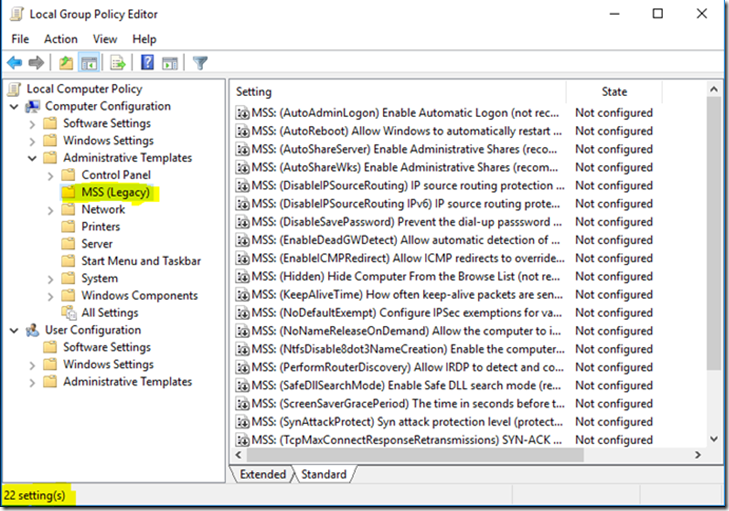
After adding the MSS templates we have 22 additional settings under the new MSS group:
After adding the SecGuide templates we have 5 new setting under the new MS Security Guide group:
Now, with all the settings available, you can configure your system using the Windows 10 STIG as a reference or simply adjusting it to your needs.
Download the latest Windows 10 STIG and load it into the STIG viewer.
I’ve selected only the CAT I rules to keep it simple.
Using Microsoft’s Administrative Templates
The new custom ADMX and ADML file reference the same registry settings as the older procedure to replace the sceregvl.inf file, but in a manner that is supportable. The files are included in the download packages with the Windows 10 and Windows Server 2016 baselines. Note that the baselines no longer include recommendations to configure many of the MSS settings that were recommended in the past, as they have no security value against contemporary threats. The few that are still configured in the baseline have limited benefit at most.
Download the templates:
Install them:
Before you get lost, use the Group Policy Settings reference guide. It’s an Excel spreadsheet that list all the information you want about all the security settings available in new Windows 10 templates. Get it here.
Make a backup copy of your existing .admx and .adml files. Add the new .admx and .adml files to the appropriate folders, or copy all the new files replacing the existing ones.
Before the installation of the templates:
- 2283 Computer configuration settings
- 1731 User configuration settings
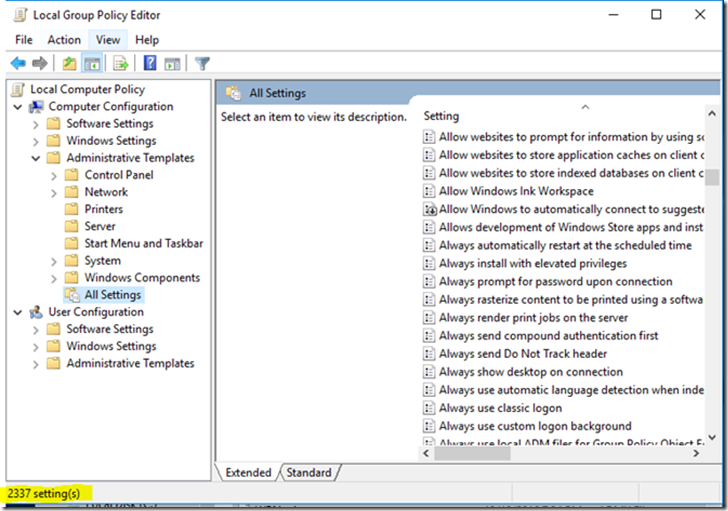
After the installation of the templates:
- 2337 Computer configuration settings
- 1773 User configuration settings
As you can see, now you have a big set of additional settings to configure all the security parameters of your Windows 10 machine. Obviously, you can use the STIG as a reference or you can use any other standard, for instance the CIS benchmarks.
Once you are done configuring your system, you can export the new settings and reapply them to other machines assuming those machines also have all the templates installed. We’ll get to that ahead in this post.
Domain GPOs
If you are installing the templates to edit domain-based GPOs, follow these steps:
Create a Central Store for ADMX files.
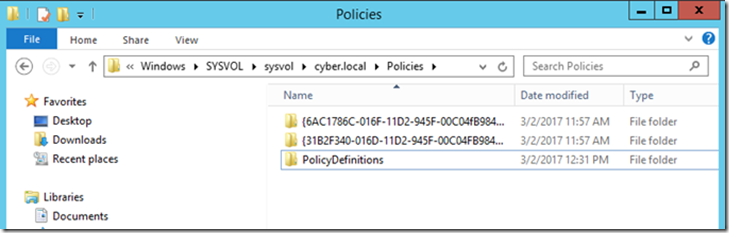
The central store is a folder structure created in the sysvol directory on the domain controllers in each domain in your organization. You will need to create the central store only once on a single domain controller for each domain in your organization. The File Replication service then replicates the central store to all domain controllers. It is recommended that you create the central store on the primary domain controller because the Group Policy Management Console and Group Policy Object Editor connect to the primary domain controller by default.
The location should be the same or similar to the path below, just replace <domain_name> with your domain name:
C:\Windows\SYSVOL\sysvol\<domain_name>\Policies\PolicyDefinitions
Select the path to install the ADMX files:
Select Next:
Complete the installation:
Once this is complete you can now create a GPO to manage the Windows 10 machines in your domain.
NOTE: In this scenario, any form of ADM/ADMX file only needs to be present on the machine where the policies are edited from, without the need to be present on every machine where these policies are applied to. The ADMX files simply link the GUI of the GPO Editor with the appropriate registry settings to make; the registry settings are simply stored and processed at each client where the GPO applies.
Using the Security Baseline
A security baseline is a collection of settings that have a security impact and include Microsoft’s recommended value for configuring those settings along with guidance on the security impact of those settings. These settings are based on feedback from Microsoft security engineering teams, product groups, partners, and customers.
There are over 3,000 Group Policy settings for Windows 10, which does not include over 1,800 Internet Explorer 11 settings. Of those 4,800 settings, only some of them are security-related. While Microsoft provides extensive guidance on different security features, going through each of them can take a long time. You would have to determine the security impact of each setting on your own. After you've done that, you still need to determine what values each of these settings should be.
To help faster deployments and increase the ease of managing Windows, Microsoft provides customers with security baselines that are available in formats that can be consumed, such as Group Policy Objects backups. You can use security baselines to ensure that user and device configuration settings are compliant with the baseline or to adjust it to your specific needs.
Get them here
The latest security baselines for Windows 10 include importable GPOs, tools for applying the GPOs, custom ADMX files for “pass the hash” mitigation and legacy MSS settings, and all the settings in spreadsheet form. It also has spreadsheets generated from Policy Analyzer that show differences from past baselines and brief descriptions of the reasons for the differences, and a similar spreadsheet listing the differences between the Member Server and Domain Controller baselines.
-
Documentation: All the settings in spreadsheet form
-
Templates: ADMX and (US English) ADML files surfacing some "pass the hash"-relevant settings through the Group Policy editor. (Note: the Local_Script folder contains scripts that install these files to the appropriate location.)
-
GP Reports: Group Policy reports formatted as HTML files (for those who prefer that format over Excel spreadsheets).
-
GPOs: Group Policy Object backups for the eleven separate sets of baselines. These can be imported into Active Directory Group Policy.
-
Local_Script: This directory contains three batch files that apply appropriate settings to the current machine:
-
Client_Install.cmd,
-
DomainController_Install.cmd
-
MemberServer_Install.cmd.
-
-
WMI Filters: This directory contains .MOF files that you can import into your Group Policy configuration to ensure that GPOs are applied only to the appropriate systems
Using the LGPO tool:
- Export
- LGPO /b <path>
- You need to create the path first
- Import
- LGPO /g <path
Now you can apply the GPOs directly to your machine or you can analyze them first with the Policy Analyzer
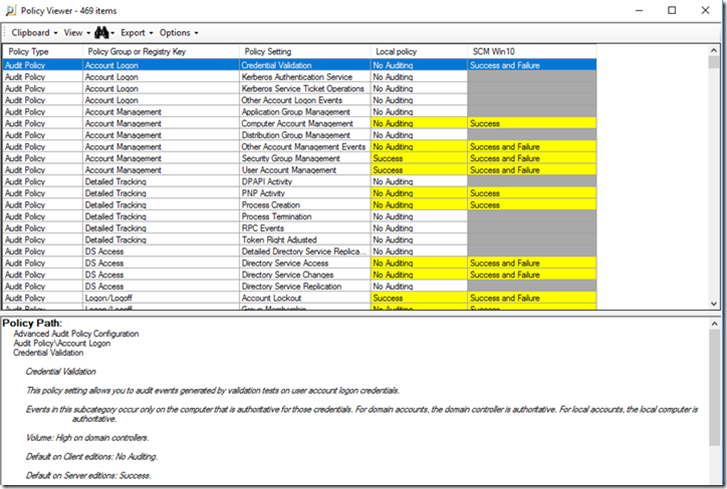
Using the new Policy Analyzer
There is a new version of the Policy Analyzer that can be tested just for the fun of it.
Get it here
Use the sample set of rules shipped with the current version of the tool.
You cannot import the Windows 10 STIG template into this tool because the STIG is now SCAP compatible and there is no .inf file available. However, you can import the GPOs from the Security Baseline and compare it with your current machine definitions.
And the result will look similar to this…
Previous post: Linux Hardening with OpenSCAP
Next post: Windows 10 Hardening (Part II)















7 comments:
Good Bolg. Oracle Fusion SCM Online Training
Thank you for sharing this post.
SAP Training in Chennai
Hardware and Networking Training in Chennai
Cloud Computing Training in Chennai
Pearson Vue Exam Center in Chennai
Oracle Training in Chennai
.Net Training in Chennai
Java Training in Chennai
Software Testing Training in Chennai
AWS Training in Chennai
CCNA Training in Chennai
I take pleasure in the comments on this blog, windows 10 activator really gives it that community feel!
nice blog very nice
please check my website : https://playbazaar.ind.in/
like your blog very nice really
please My Play Bazaar Website Check
; https://playbazaar.ind.in/
This is an excellent post I seen thanks to share it. It is really what I wanted to see hope in future you will continue for sharing such a excellent post.
call center solutions in Nigeria
This is my first time i visit here and I found so many interesting stuff in your blog especially it's discussion, thank you.
click here
puppies for sale near me
yorkie puppies with home training
where to buy Yorkie
Yorkie Female Puppies for sale
Yorkie puppies ready for their forever homes
welcome to yorkie puppies nearme
Post a Comment